* open http://jwt.calebb.net/ ```javascript eyJ0eXAiOiJKV1QiLCJhbGciOiJSUzI1NiIsIng1dCI6IlZXVkljMVdEMVRrc2JiMzAxc2FzTTVrT3E1USIsImtpZCI6IlZXVkljMVdEMVRrc2JiMzAxc2FzTTVrT3E1USJ9.eyJhdWQiOiJodHRwczovL2dyYXBoLndpbmRvd3MubmV0LyIsImlzcyI6Imh0dHBzOi8vc3RzLndpbmRvd3MubmV0L2M4MjgwNGViLTkzODgtNDJiOS04ZjI4LWM2N2Y2MjNiMjY5MS8iLCJpYXQiOjE1MDE3MjIyOTIsIm5iZiI6MTUwMTcyMjI5MiwiZXhwIjoxNTAxNzI2MTkyLCJhY3IiOiIxIiwiYWlvIjoiWTJGZ1lDaTN0clU4TXpISDhPYmZOcE9nNGpscmVmTVNEMTY2TldleWk4ZnZOQW5uSzhJQSIsImFsdHNlY2lkIjoiMTpsaXZlLmNvbTowMDAzNDAwMTg0MzkxNEVFIiwiYW1yIjpbInB3ZCJdLCJhcHBpZCI6IjgwMTA0ZTkzLTdhZDMtNGUwZS1hMDBhLTYwNjlhZjYxZTI4YyIsImFwcGlkYWNyIjoiMCIsImVfZXhwIjoyNjI4MDAsImVtYWlsIjoibm9vYmVydEBnbWFpbC5jb20iLCJmYW1pbHlfbmFtZSI6IkdlbW9sbCIsImdpdmVuX25hbWUiOiJUb255IiwiaWRwIjoibGl2ZS5jb20iLCJpcGFkZHIiOiI5OC4xNDQuMTExLjIzMyIsIm5hbWUiOiJUb255IEdlbW9sbCIsIm9pZCI6ImRhMTE2NjMyLTNhN2UtNDY4NC05ZTFlLTkzYzMyNzRhZDU2MyIsInBsYXRmIjoiMiIsInB1aWQiOiIxMDAzQkZGRDg2NkI2RkJGIiwic2NwIjoiVXNlci5SZWFkIiwic3ViIjoiMnliMXltU196WENXUDl0OE5LMmE4N1hHUjJxWkJYWjlEWW84U01IWWFSTSIsInRlbmFudF9yZWdpb25fc2NvcGUiOiJOQSIsInRpZCI6ImM4MjgwNGViLTkzODgtNDJiOS04ZjI4LWM2N2Y2MjNiMjY5MSIsInVuaXF1ZV9uYW1lIjoibGl2ZS5jb20jbm9vYmVydEBnbWFpbC5jb20iLCJ1dGkiOiJlaG1JbW9rQ2VFLXlYVGxxUUJRQUFBIiwidmVyIjoiMS4wIn0.QvPzu3t2FyOen1CPfqskLFxtZOqfLti1I51nAPtk0rM5735OtNyInl5pGidHQIaizWfMN0mHz67fHMRFAY1h1M-SLjIQCvrUN17-koroWAuSrAu9aqSnaVm0BfmoEUh3GnWuWsbWWW0Kh_yZgQDsFUYL1pu17ZKUhOZkFfRGE7RM9hXHNcv5fUl-tDUEFucMCo_MCJavK2nF2mi5g3V9R0xR3jJ3zAPYvStlLqXGE-WgfIUf-ORf8bd-CNvRL2zz1G1aFcx15gyyD99qdrR8Q14uHyrLjjkLAbmtakbDIs-o8C9q2yE3vY6mcxiJapceQs5GzSFC_KSmr6sla_O5IA ``` ```javascript eyJhbGciOiJSUzI1NiIsImtpZCI6InltRVlEeEMyX3N3RmdHQlFIbzdzajFOczFHR1gxY3JyY3FZc3ltTURvTE0ifQ.eyJ2ZXIiOjEsImp0aSI6IkFULjFEaUZuZTJfLWRldURMSGNtY0txbGk3aHBDbzBKZUpWbzVNdEhZZ3N0VlUuczBFYXlrcTV0YjNrMEdTdWlnbXY3UTJteGJjWE5hZ25NL2FGNDhtMDU1Zz0iLCJpc3MiOiJodHRwczovL2Rldi0xMDAwNDAub2t0YXByZXZpZXcuY29tIiwiYXVkIjoiaHR0cHM6Ly9kZXYtMTAwMDQwLm9rdGFwcmV2aWV3LmNvbSIsInN1YiI6IlRlc3RGYWNlQGRldndpLmNvbSIsImlhdCI6MTUwMTcyMjEwNCwiZXhwIjoxNTAxNzI1NzA0LCJjaWQiOiIwb2FiMWZxdmR5VjluRDJHUDBoNyIsInVpZCI6IjAwdWIxamowaXEwSHVNWEZ0MGg3Iiwic2NwIjpbImdyb3VwcyIsIm9mZmxpbmVfYWNjZXNzIiwib3BlbmlkIiwiYWRkcmVzcyIsImVtYWlsIiwicGhvbmUiLCJwcm9maWxlIl19.An9j2oyHfRizs9xTpyyYrMJXPY2ZVgHlfQ5LHADOY3My-7t5zGO4aKCnCPLMisLOT2MNxyCN8EBTtKB0FkeDFXu9KUusrVpEcvv9Fp18tLZE-3jpBs2zsHzX5GM9tOOS-m5skUCVK0amnIsKcfdSQsGqZAgLxzZiSgjxygabslrj9OEeKiBKzQEJb2j2h6DT57QSNWASXnM8Cre0Kby3oDlVPtdbEX7sQdWjH7_fXxUsesNt65ALUSJFIacVVVTb0-JfCGyaMC6-0huLI_kVjlvqtT8IeASJ1zWdEzrK1gYM93c7fMr2da9GaUOqLczj3sPyzSYutNW5XRZjDk2GZg ``` * npm start, s * open hapi sample, start it, open web page * Open Azure RN AD sample * Open okta demo testface@devwi.com QWEqwe123
## Securing your campground with JSON Web Tokens (JWTs)<!-- .element: style="margin-top: 300px; color:white;text-shadow: -1px 0 gray, 0 1px gray, 1px 0 gray, 0 -1px gray;" -->
 Note: * Beer tasting
## Who am I?  <!-- .element: style="width: 200px;" --> * Tony Gemoll - @Oobert - tony.gemoll@gmail.com * Enterprise Architect at Northwestern Mutual * Organizer of Milwaukee JavaScript User Group
## Warning! * This is an intro * Code, is demo code * Security is hard, Do your homework
## Cookies, quick recap * Cookie holds session ID * Session state stored on server Note: * Hard to share cookies across domain * scaling issues, session state storage
## Why JWTs? * JWTs require no server state * CORS * CSRF protection if stored in local storage * Native mobile friendly Note: * Can scale horizontal * CORS enable api, easy sharing * Cross site request forgery * Short life span of JWT * Native mobile and cookies is a mess
## What's a JWT?! * JSON Web Token (JWT) is an open standard (RFC 7519) that defines a compact and self-contained way for securely transmitting information between parties as a JSON object. Example: ```javascript eyJ0eXAiOiJKV1QiLCJhbGciOiJSUzI1NiIsIng1dCI6InowMzl6ZHNGdWl6cEJmQlZLMVRuMjVRSFlPMCIsImtpZCI6InowMzl6ZHNGdWl6cEJmQlZLMVRuMjVRSFlPMCJ9.eyJhdWQiOiJodHRwczovL2dyYXBoLndpbmRvd3MubmV0LyIsImlzcyI6Imh0dHBzOi8vc3RzLndpbmRvd3MubmV0LzZlZGRkMTg1LTdhZDctNGVlMy05NDgxLTA0NjQ0YjlmNDNhMi8iLCJpYXQiOjE0OTQ1MTExNjksIm5iZiI6MTQ5NDUxMTE2OSwiZXhwIjoxNDk0NTE1MDY5LCJhY3IiOiIxIiwiYWlvIjoiWTJaZ1lHanV1SnQ4K20rZVg2REtYTDJpYzMveUZqRVZPeHZ4ZkQ5cXd2N3BncHF5RlE4QSIsImFtciI6WyJwd2QiLCJyc2EiLCJtZmEiXSwiYXBwaWQiOiIzNzk1MmFhNS1hMGZmLTQ1NjgtYjI2ZC1iZGE5YTE5NDI5MDIiLCJhcHBpZGFjciI6IjAiLCJkZXZpY2VpZCI6ImZiYTdjZDg2LTIwMGItNGJmZi1hNjJkLTEyN2Q4NmZjNjgyOCIsImVfZXhwIjoyNjI3OTksImZhbWlseV9uYW1lIjoiR0VNT0xMIiwiZ2l2ZW5fbmFtZSI6IkFOVEhPTlkiLCJpcGFkZHIiOiIyMTYuMjAuMTc2LjE0IiwibmFtZSI6IkdFTU9MTCwgQU5USE9OWSIsIm9pZCI6ImVkMzY3MjJmLWFiZmEtNDI4OS1hN2ZmLTdmOWZlZmU2YjM5OCIsIm9ucHJlbV9zaWQiOiJTLTEtNS0yMS0xMzYzODgyMDIwLTMwNzY0NTY2MDgtMjI4MDA2NjA2Mi0xMDMxNjIxMCIsInBsYXRmIjoiMSIsInB1aWQiOiIxMDAzN0ZGRTk4NjQ4OEM0Iiwic2NwIjoiVXNlci5SZWFkIiwic3ViIjoic2hPeGtIMDFIeGVnMzZHeU85SnRJb1hfdG0ydk0yTWhwM2hSX3picWl4cyIsInRpZCI6IjZlZGRkMTg1LTdhZDctNGVlMy05NDgxLTA0NjQ0YjlmNDNhMiIsInVuaXF1ZV9uYW1lIjoiYW50aG9ueWdlbW9sbEBubWNvcC5jb20iLCJ1cG4iOiJhbnRob255Z2Vtb2xsQG5tY29wLmNvbSIsInV0aSI6IkZlOHhHeDU4TUVLdkJTSkxBZ3NNQUEiLCJ2ZXIiOiIxLjAifQ.mEiGaBU8GfBP-H8ywDBwi0uofEJrpjT3LH0jr-SZPOhSE987LJlucXwTtzpviZeutHnFY_bcZBM-fxdcIPoQNdcd2KIcwkFj9avjScIXRh8fOQW0EpOafONtsNQNrsyvHkP7iUFMqpPFDc4N1HmPWe3Kjl1Negdfz5P2zR9lk47oGBsjVe4UzsUeQyha6U8qYp3pnHjgs4AxN10lNBnD2g6rC1_-3m-VaVfkNY3-ZAUUpEeqb_RCHAFf3XnQiBGaPHeagEFkb7XjLWWopgTrsLnZxGORWkuDcv_BcTJfjqFJjXH8-nSXv2KJn1EhxdktAnGGad5gGuIMVQkh88iwQA ``` Note: * Explain: * Compact * Self contained
## The JWT is a lie So is the bacon... maybe...
## The JWT is a lie 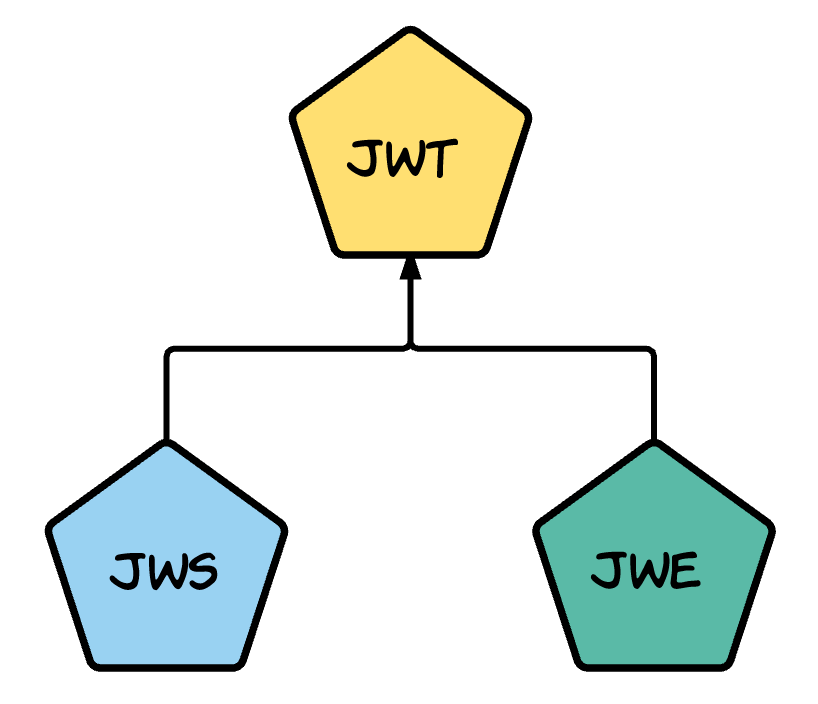 <!-- .element: style="height: 40vh;" --> Note: * No such thing as JWT * JWS - JSON Web Signature * Payload not encrypted * JWE - JSON Web Encryption * Payload encrypted * Javascript Object Signing and Encryption (JOSE)
## What's a JWT?! * Has 3 parts... * Header * Payload * Signature
## What's a JWT?! ### Header ```JSON { "typ": "JWT", "alg": "RS256", "x5t": "z039zdsFuizpBfBVK1Tn25QHYO0", "kid": "z039zdsFuizpBfBVK1Tn25QHYO0" } ```
## What's a JWT?! ### Payload ```JSON { "aud": "https://graph.windows.net/", "iss": "https://sts.windows.net/6eddd185-7ad7-4ee3-9481-04644b9f43a2/", "iat": 1494510286, "nbf": 1494510286, "exp": 1494514186, "appid": "37952aa5-a0ff-4568-b26d-bda9a1942902", "deviceid": "fba7cd86-200b-4bff-a62d-127d86fc6828", "family_name": "GEMOLL", "given_name": "ANTHONY", "name": "GEMOLL, ANTHONY", "oid": "ed36722f-abfa-4289-a7ff-7f9fefe6b398", "scp": "User.Read", "unique_name": "anthonygemoll@northwesternmutual.com", "upn": "anthonygemoll@northwesternmutual.com", "uti": "J77mOxlQt0O-UDR10jAOAA", "ver": "1.0" } ``` <!-- .element: style="width: 1100px" -->
## What's a JWT?! ### Signature ```JSON mEiGaBU8GfBP-H8ywDBwi0uofEJrpjT3LH0jr-SZPOhSE987LJlucXwTtzpviZeutHnFY_bcZBM-fxdcIPoQNdcd2KIcwkFj9avjScIXRh8fOQW0EpOafONtsNQNrsyvHkP7iUFMqpPFDc4N1HmPWe3Kjl1Negdfz5P2zR9lk47oGBsjVe4UzsUeQyha6U8qYp3pnHjgs4AxN10lNBnD2g6rC1_-3m-VaVfkNY3-ZAUUpEeqb_RCHAFf3XnQiBGaPHeagEFkb7XjLWWopgTrsLnZxGORWkuDcv_BcTJfjqFJjXH8-nSXv2KJn1EhxdktAnGGad5gGuIMVQkh88iwQA ```
## Verification of a JWT ### Signature * key signed tokens * well known endpoint * kid * JWK * passphrase signed token
## Verification of a JWT ### Payload * audience claim * expiration time * issuer claim * nonce
## Claims ### Payload * Not a state store * Only put what you need * Keep performance in mind
## Storage * Local storage * Session storage * Cookies
## A note on OAuth * OAuth vs OpenId * What about OpenId Connect? * Many IDPs follow the OpenId Connect spec Note: * OAuth is for Authorization ** Get a key to access an api * OpenId is for Authentication ** Get a token that represents the user * OAuth can be abused for Authentication and will cause issue * OAuth and OpenId merged under OpenId Connect in 2014
## DEMOS * DIY JTWs * 3rd Party IDP on mobile (Azure AD) * 3rd Party IDP with SSO on mobile (Azure AD) * 3rd Party IDP with 2FA on mobile (Okta)
## Demo Recap Note: * Webview credential entry * MFA security, txt sucks * Doing MFA yourself, Speakeasy
## Need more JWTs? * JSON WEB TOKENS WITH AUTH0 FOR YOUR MICROSERVICE ARCHITECTURE * Chris Gruber * 2:30pm Today in room D Note: * Auth0 * OAuth Grants * Micro Services
## Links! * https://medium.facilelogin.com/jwt-jws-and-jwe-for-not-so-dummies-b63310d201a3 * https://auth0.com/blog/cookies-vs-tokens-definitive-guide/ * http://jose.readthedocs.io/en/latest/ * https://twitter.com/justin/status/883171036283285508 * https://docs.microsoft.com/en-us/azure/active-directory/develop/active-directory-token-and-claims
## more links! * https://ponyfoo.com/articles/setting-up-2fa-for-nodejs-applications * https://github.com/dwyl/hapi-auth-jwt2 * https://github.com/northwesternmutual/azure-activedirectory-library-for-react-native * https://github.com/oktadeveloper/okta-openidconnect-appauth-ios
## Questions?? * Tony Gemoll - @Oobert - tony.gemoll@gmail.com * Enterprise Architect at Northwestern Mutual * Organizer of Milwaukee JavaScript User Group